Do you or someone you know love to solve problems and help people with their technology? Looking for variety and ...
Do you or someone you know love to solve problems and help people with their technology? Looking for variety and ...

What is the value of moving to the #cloud? Give us your thoughts in the comments. @Microsoft CTO top lists ...
When the holiday season rolls around, it’s not just Santa Claus that’s coming to town. Scammers, hackers, bots and all ...
With all the password requirements nowadays, complexity requirements, expirations, lockouts, etc., it is nearly impossible for anyone to remember all ...
Many business owners take for granted the quality of a Personal Computer (PC) purchased for their business. The traditional belief ...
Have you ever sent someone a password in an email? Chances are your answer is you have. We all know ...
For most business owners, the prospect of choosing a good Managed IT Services Provider (MSP) to set up and/or manage ...
You’re working on your computer, it’s halfway through the second week of the month, and all of a sudden, your ...
With relentless reliance on dependable phone systems for day-to-day operations in pretty much every business sector, even considering the potential ...
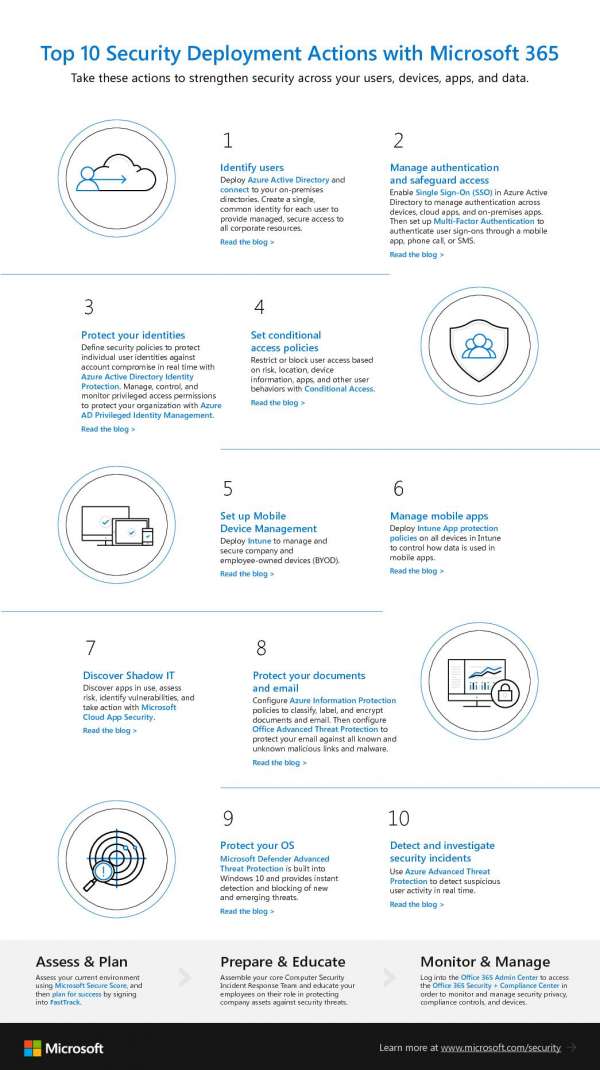
For nonprofits, your mission is critical. Don't let security issues get in the way! #Microsoft 365 can make security management ...